What is Wireguard?

WireGuard is a new VPN protocol that has been making waves in 2018. It’s an up-and-coming player on the block, but what's so great about it? We'll give you all of its pros and cons right here!
As we know, a VPN protocol dictates exactly how a VPN handles data and is a blueprint for everything a VPN does, so it’s important to know all their characteristics in order to make the best choice for our particular needs.
Table of contents
- 1 What is Wireguard?
- 2 How does Wireguard work?
- 2.1 Wireguard VPN technical analysis
- 3 Is Wireguard safe to use?
- 4 How Fast is Wireguard VPN protocol?
- 5 Wireguard Pros and Cons
- 5.1 Wireguard Pros
- 5.2 Wireguard Cons
- 6 Wireguard vs other VPN protocols
- 6.1 Wireguard vs PPTP
- 6.2 Wireguard vs L2TP
- 6.3 Wireguard vs IKEv2
- 6.4 Wireguard vs SSTP
- 6.5 Wireguard vs OpenVPN
- 7 Bottom line
What is Wireguard?
WireGuard is an open-source VPN that uses state-of-the-art cryptography while at the same time being easy to configure, fast, and secure. It is a new VPN protocol that started as an experiment. It gradually evolved as an OpenVPN and IPSec alternative (considered by many as being difficult to configure and manage properly).
Wireguard code is written in less than 4000 lines of code, thus making the code easy to audit and read for everyone.
WireGuard aims to provide a general-purpose VPN technology that is more secure, simpler, and faster. It can be deployed easily on anything from high-end servers to low-end devices (such as Raspberry PI).
WireGuard was officially released publicly on March 30th, 2020, is included in version 5.6 of the Linux kernel.
Although WireGuard was originally developed for Linux, it can now provide VPN on macOS, VPN on Windows, VPN on Android, VPN on iOS, or BSD.
How does Wireguard work?
WireGuard uses modern cryptography and network code to create an encrypted tunnel between two devices. Using some clever strategies, it even works when the client device’s IP address changes. For example, you can switch from mobile data to Wi-Fi without waiting thirty seconds for the VPN to reconnect.
It works pretty similar to SSH (Secure Shell). Basically, it exchanges public keys. Once they’re exchanged and the app-server tunnel is established, there’s no need to keep managing the connection. Also, once WireGuard establishes the VPN tunnel, the server must receive at least one encrypted data packet from the client before it can actually use the session. That ensures proper key confirmation.
Wireguard VPN technical analysis
- 1. Wireguard uses the following protocols and primitives:
- - ChaCha20 for symmetric encryption, authenticated with Poly1305, using RFC7539's AEAD construction
- - Curve25519 for ECDH
- - BLAKE2s for hashing and keyed hashing, described in RFC7693
- - SipHash24 for hashtable keys
- - HKDF for key derivation, as described in RFC5869
- 2. The protocol is stealthy, as it does not respond to any packets from peers it doesn’t recognize, so a network scan will not reveal that WireGuard is running on a machine. Furthermore, the connection between peers, which can act as both clients and servers at the same time, goes silent when there’s no exchange of data.
- 3. It has a smaller attack surface compared to other VPN projects and, since it doesn’t respond to unauthenticated packets, it’s much harder to attack.
- 4. WireGuard only works on UDP and doesn’t officially support TCP
- 5. Wireguard offers a lighter built than any VPN protocol as it uses around 4000 lines of code, unlike other protocols like OpenVPN which uses over 70000 lines of code.
Is Wireguard safe to use?
Many security experts and WireGuard’s own team consider it stable. This was already the case before March 2020, when it was initially implemented into the Linux 5.6 kernel.
It is generally believed that WireGuard’s security as a protocol and its implementation in the Linux kernel is superior to other alternatives. Project age and code audits serve as signals for decision-makers, but there are other, often stronger signals as you delve deeper.
The cryptographic primitives used, the fact that it can be implemented without dynamic memory allocation, and the protocol state machine’s simplicity are all arguably equally or even more useful.
WireGuard’s simpler code base makes it much easier and less time-consuming for security auditors to check the integrity of this protocol. For example, one person could do all their work within a few hours if they know what they are doing!
The only issue present for commercial VPN users was the fact that Wireguard VPN stores endpoint IP addresses but since the code is very light this was easily removed by VPN providers or used a double NAT system to ensure privacy level doesn’t decrease. You needn't worry, HideIPVPN has this all covered, there is no endpoint IP exposed.
How Fast is Wireguard VPN protocol?
Original benchmarks estimated that the protocol is much faster than OpenVPN and IPSec. Since then, numerous VPN review sites and tech blogs have tested WireGuard speeds compared to other protocols.
Wireguard is optimized to use multiple processor cores at the same time, and it uses faster encryption methods.
To get a better grasp on the speeds check the graph below where you can compare Wireguard VPN speed to other VPN protocols speed characteristics:
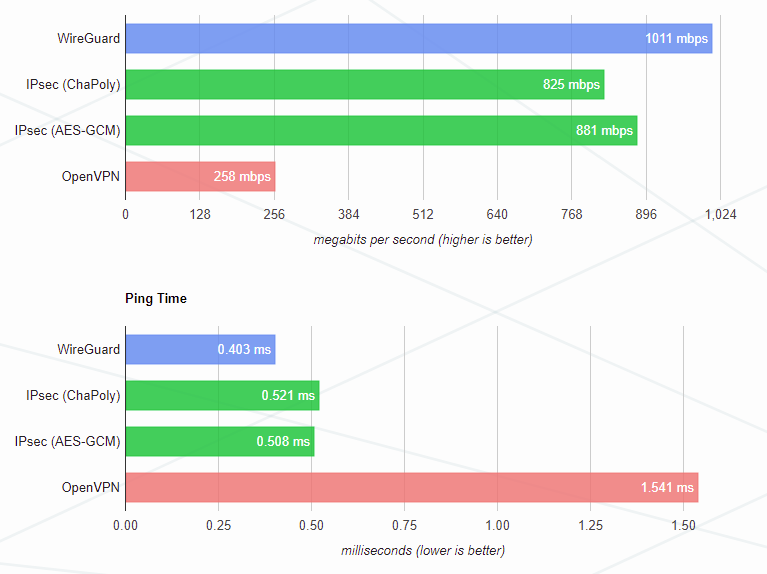
These tests have been conducted on Intel Core i7-3820QM and Intel Core i7-5200U
Machine with similar configuration characteristics in terms of encryption. You may notice that OpenVPN is the slowest, it’s because it uses the most resources and has maxed out the cpu. This means that Wireguard uses CPU cores very efficiently as part as one of the perks that makes it so fast.
Best speeds can be achieved by Linux users as Wireguard VPN is built in the Linux Kernel, unlike other operating systems, offering the best possible results this protocol can provide.
Wireguard Pros and Cons
Pros:
- 1. Performance
WireGuard is type of fast VPN protocol as it uses high speed cryptographic primitives (More than 1000Mbps in terms of through put). And also because of the fact that it executes its processes inside the kernel module of Linux, it is supposed to provide faster performance and bandwidth among all the protocol solutions. This recommends WireGuard to be used in embedded devices such as the smartphone and home routers.
- 2. Configurations
Most at times, WireGuard does not require a certificate infrastructure because it uses Public keys only. That too for the purpose of identification and encryption. This makes every particular software easy to configure in WireGuard.
- 3. Security
For providing high secure online connection, WireGuard uses a cryptographic key routing process. It does not follow the industry standard AES-256 encryption techniques. In here authorized VPN IP addresses are combined with Public encryption keys for better security.
- 4. Code base
WireGuard uses only about 3800 lines of code which is very few compared to OpenVPN and IPSec. This lean coding structure ensures protocol easier to get an audit so that it can experience the least number of vulnerabilities. - 5. Platform support
WireGuard has the capability to support most of the platforms out there. Currently, Wireguard supports Windows, Android, IOS, Mac OS, and Linux.
Cons:
- 1. WireGuard only works on UDP, so you can’t use it over TCP port 443 (the HTTPS port). So network admins could block WireGuard if they block the UDP ports it uses (there’s a lot of them, though).
- 2. Endpoint IP logs store, but it has been easily bypassed by removing this option from original code. You needn't worry, HideIPVPN has this all covered, there is no endpoint IP exposed.
Wireguard vs other VPN protocols
Wireguard vs PPTP
Just like Wireguard, PPTP is a fast VPN protocol good for activities like streaming. However, it’s outdated and not recommended for the security-conscious.
Unlike PPTP, Wireguard is open-source so it can easily be checked and properly audited. In terms of security Wireguard will be a better choice as NAT Firewalls can easily block PPTP. While Wireguard can be blocked too it’s highly unlikely for network admins to blocks most of UDP ports just to restrict it.
Also, right now Wireguard is already more supported on devices since some platforms, like iOS, have dropped support of PPTP protocol.
Wireguard vs L2TP
While both of them offer a good security outlay, Wireguard uses newer algorithms and more complex encryption techniques. Unlike Wireguard, L2TP doesn’t offer any security by itself and is used in conjunction with IPSec for authentication and encryption.
L2TP/IPsec uses 3 ports (UDP 500, UDP 4500, and UDP 1701) and ESP IP Protocol 50 thus making it more vulnerable to be blocked by networks admins whereas Wireguard can use any UDP port is free on the server it’s deployed on and there are 65535 UDP available ports.
Wireguard vs IKEv2
While IKEv2 is also a fast and fairly new protocol, WireGuard has two advantages: its encryption primitives may be faster, and it is built into the Linux kernel. Most tests show that WireGuard is more consistent in speed. The difference between IKEv2 and WireGuard is that most devices support the former by default. Also, Wireguad offers a more modern encryption library and is a bit less CPU intensive. Like L2TP/IPSec, IKEv2/IPSec is easier to block because it uses fewer ports: UDP 500, ESP IP Protocol 50, UDP 4500. On the plus side, IKEv2 offers MOBIKE – a feature that lets the protocol resist network changes. So if you switch from WiFi to mobile data on mobile, your VPN shouldn’t disconnect.
Wireguard vs SSTP
When it comes to this comparison we should begin by mentioning that Wireguard is open source and SSTP is not, and since SSTP was created by Microsoft, there is no external third-party review. This means that there may be backdoors built into the code, which can compromise overall security. Other platforms and operating systems can implement SSTP, but the support is poor. On the plus side for SSTP is that it uses TCP port 443 which is the HTTPS port, so network admins cannot easily block it, but Wireguard uses any UDP port available so it kind of evens out in these terms.
WireGuard actually works on more platforms since macOS and iOS don’t support SSTP out of the box. If you want security, guaranteed privacy, and speed, then stick to WireGuard.
Wireguard vs OpenVPN
This is perhaps the most popular comparison on the web between Wireguard VPN and other VPN protocols. Both OpenVPN and WireGuard are open source, have almost no loopholes, and require additional configuration files to be set on most devices. The difference is that WireGuard uses a more advanced encryption library and is more efficient. Most done tests reveal that WireGuard beats OpenVPN by about 15% under normal conditions. When OpenVPN was restricted to the slower TCP mode, WireGuard's speed increased by 56%. Although the best case comparison is not an exciting difference, you will definitely feel WireGuard's speed increase, especially in the case of large downloads. For individuals, is WireGuard better than OpenVPN? It depends on your needs. WireGuard is simpler, faster, and easier to set up than OpenVPN, but it is not yet available for some devices. For example, if you have an old router for router-based VPN, you may have to stick to OpenVPN. Wireguard’s code base is much more lightweight (roughly 4,000 lines compared to 70,000 – 600,000 lines), and it uses CPU cores more efficiently. In our tests, WireGuard was faster even when we used OpenVPN over UDP.
Since OpenVPN was the overall first choice due to speeds and security you can firmly go for Wireguard now as it does everything OpenVPN does, but much better.
Bottom line
To sum up some answers to the question - What is Wireguard?, we believe Wireguard should be your first choice nowadays due to the following facts:
- - Much simpler to set up, especially for server-side
- - You never have to worry about losing connection
- - Much quicker to establish a VPN connection
- - Significantly less battery drain on mobile devices, especially when using a custom Kernel that has the Wireguard module
We believe that WireGuard is part of the VPN future and this is why HideIPVPN has implemented this protocol. We hope you enjoy it!



