Top 10 VPN Security Risks
Last updated on March 1st, 2022 in VPN

VPNs are an excellent way to protect your Internet traffic and privacy from government surveillance, ISP snooping, or nosy hackers.
The only problem? You may be exposing yourself to too much vulnerability with the VPN if you don’t take precautions – these are VPN security risks!
Here’s all about how this works in detail so that can avoid any problems later down the road.
Table of contents
With so many options available, finding a reliable VPN is more difficult than ever.
The good news? There are plenty of great security providers out there to choose from! The bad? Not all will protect you as they should – some pose serious risks and dangers even if their service seems otherwise safe-looking at first glance or during testing phases (such as SpeedTest). You don’t want this article’s list to be what separates someone who gets hacked from another person in the same boat but with better research skills.
When it comes to privacy and security, there are a lot of pitfalls that you might fall into if not careful. The following list includes some dangers associated with selecting an unsecured VPN:

A VPN log policy is a document that outlines the specific requirements that must be met in order for a VPN to be used. This document can include things such as acceptable usage policies, logging requirements, and security protocols. Having a VPN log policy in place can help ensure that all users of the VPN are aware of the expectations and requirements and that any violations can be quickly identified and addressed.
When creating a VPN log policy, it is important to consider the specific needs of your organization. For example, you may want to require that all users of the VPN are authenticated and that logs are kept of all activity. You may also want to specify the types of data that are allowed to be transmitted through the VPN.
While this is a good practice for a private company in-house VPN, it’s the worse thing you can have from a commercial VPN.
Using a VPN is pointless if the provider keeps logs of your browsing activity. This could lead to severe security risks, and you would have no way of knowing that they were monitoring or accessing this data since it’s not available in an understandable format on their website anyway (unless there’s some secret sauce behind how they do things).
The best VPN for privacy is a zero-log policy. If you want to enjoy online freedom and peace of mind, then this type should be your go-to option!
The devil is always in the details and this holds true for VPN providers as well. A company could claim they respect your privacy while gathering extensive data on you through loggers or even injections; but if there’s anything that’ll draw attention away from these practices (such), it would be their own policy statement which clearly states whether any sort of logging takes place at all–and when read carefully…well let’s just say you shouldn’t get so excited about such a provider.
VPNs are not just for privacy purposes, they can also offer security and anonymity when browsing the internet. However some providers have strange policies about their data collection which may or might not be mentioned in detail within your chosen VPN’s Privacy Policy – so you need to read these carefully! Free alternatives will typically share user information with third parties (AKA advertisers).
In such cases, the data you provide will be used by advertisers to create personalized profiles and spam your users with targeted ads. In some cases, they might even display these advertisements through their VPN clients!
Third parties will want to know about your personal information, so it’s important that the advertisers and any others who buy data do some background checking. If they don’t care enough for you then there may come a point where cybercriminals get their hands on this sensitive data too. This is why it’s a good practice to have both VPN and Firewall together in the same mix.
VPNs are an essential part of any online security strategy, but they’re not perfect. In fact, the encryption that protects your data can be weakened by poor configuration and maintenance practices – this includes free services!
A leaky VPN could pose serious risks to you as well as those around them with sensitive information leaking out into plaintext without even knowing why or how much was exposed during transmission because there might not have been enough effort put into making sure everything is tight before launching live.
Before you can be the judge of that you need to learn more about what is VPN encryption and how it affects your connection.
VPNs are a great way to protect your privacy and security, but there’s always the chance of leaks. If you’re concerned about whether or not this will affect any aspects of performance for whatever reason- don’t worry! We’ve got some solutions below:
DNS Leaks and WebRTC Leaks are the most common tests you can do that will reveal if your provider poses any VPN security risks.
VPN providers are not immune to leaks and when a VPN connection is configured poorly, your data can be exposed. But it could also happen because of browser-related issues like plugins or settings on devices you use for surfing that may compromise security measures otherwise enabled by the provider’s software. You can always do a WebRTC Leak test or DNS Leak Test just to be sure.
There are many serious risks involved in using a VPN, such as malware being injected into your device when you download the client. This will start spying on what sites and apps appear forked into it- potentially giving away personal details or even infecting other parts of our computer system with ads that can be spammy at times!
Ransomware is becoming more and more popular, with some people even being asked for large ransoms in exchange for their data. This isn’t something new though; back in 2017 many free VPN services on Google Play Store were found to be malicious as well.
To emphasize this one we will provide you with the most basic example of what this is a VPN security risk. PPTP protocol is a protocol that might be fast and convenient, but it’s extremely dangerous to use if you value your privacy. The NSA has already decrypted some time ago PPTP traffic so cybercriminals know how important this vulnerability can get for them when targeting potential victims with their attacks because of its ability in providing sensitive information such as emails or banking credentials without even realizing it!
When it comes to protocols, L2TP/IPSec is not very reliable as well. In fact, the Snowden leaks show that Microsoft co-developed this protocol with Cisco and was one of several companies involved in the PRISM surveillance program – a risk for your information if you use them.
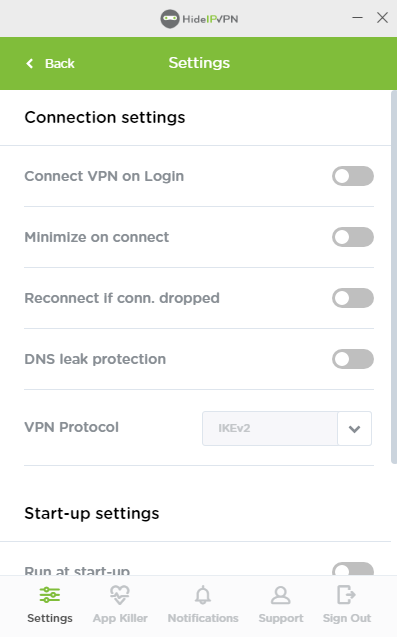
Look for a VPN provider that allows you to use stronger and safer protocols like IKEv2, OpenVPN, SoftEther, or Wireguard on top of protocols like PPTP or L2TP/IPSec.
If you’re not careful, your IP address could be used by others to access movies or other content that might belong in the privacy of their home. This is why it’s important for users who use a VPN–to protect themselves against snooping outside connections with this technique.
When a VPN provider runs their network off of users’ bandwidth and IP addresses, they are essentially taking advantage. But many people don’t realize this because the provider’s post-ToS explicitly say “we will not use your information for any other purpose than as stated within these Terms”.
This means that a cybercriminal could do illegal stuff online while using this tool and remaining anonymous themselves – downloading torrents for example! If there were more people doing such things then our network speed might decrease significantly as well because of increased traffic from these downloaders which would reduce streaming quality over video platforms like YouTube etc.
When it comes to security, a VPN with good encryption and no-log policy will do you just fine. However, if there are other features that make your life easier or more convenient then we recommend looking into these too. This was not a standard of the industry when it started but it’s a must-have nowadays from a reputable VPN provider. These might include:
With some VPNs, you might notice that your internet speed is slowing down. This can be frustrating when it’s not intentional and due to poor quality settings on the provider’s end. This usually happens with free VPN providers or free plans on premium VPN providers that are aggressively converting you to a paid customer.
You should opt for a provider that will provide you with a free trial, no credit card included that will let you test their premium service with no strings attached.
When you connect to a VPN server, you want to make sure that is encrypted providing you with the most possible secure connection. Whilst VPN encryption is important, the industry standard is using SSL for each of their servers since most of them are attached to a domain name.
You can test domain name for SSL certificate and see if it hasn’t expired yet. An expired certificate means your data may be transmitted between you and the VPN server in plain text, rather than coded.
HideIPVPN offers a VPN service with military-grade encryption, and high-speed servers with unlimited bandwidth.
Our service comes with shared IP addresses so that your activity can never be tied to one particular user, further protecting your privacy.

We also offer DNS leak protection, a Kill Switch, the latest VPN protocols, and a guaranteed no-log policy.
Every purchase you make comes with a 30-day money-back guarantee.
It’s not always a bad idea to pick a VPN that has its headquarters or servers in Five/Nine/Fourteen Eyes countries. However, your privacy will only be at risk if said service keeps logs of what you do online and publishes them without permission. So a no-logs policy is more than enough for your safety. Most of the VPN companies located overseas ( like Panama ) go to tax-friendly countries and want to promote this as privacy enchantment when in reality it’s just a monetary problem.
Zero-log policies are the best way to keep your data safe and secure. Even if a country’s government tried to force an internet provider into giving up user information, they wouldn’t have any of that person’s personal details anyway because it doesn’t exist!
VPNs are a safe and effective way to protect your privacy, but not all providers go the extra mile. If you use one of these risky VPN services it’s important that they offer good security practices. Otherwise, you risk exposing yourself to vulnerabilities in their networked software which may lead hackers into obtaining personal data about users like passwords for different accounts on social media platforms etcetera.
These are the main risks you expose yourself to by using a VPN with security risks: